zeroRISC builds hardware security infrastructure for embedded RISC-V systems — from silicon root of trust to verified firmware.
Every layer of the zeroRISC platform is designed from first principles for RISC-V hardware security.
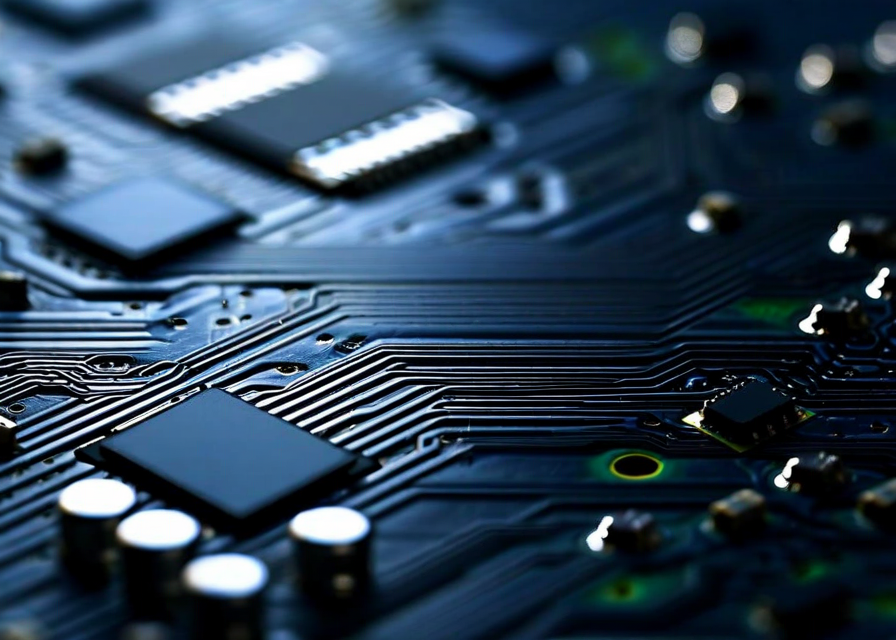
The zeroRISC platform delivers a complete security stack from the silicon up. Our RISC-V-native root of trust provides cryptographic anchoring that cannot be bypassed at the software layer, giving you a verifiable foundation for all higher-level security guarantees.
Learn about the platformSecurity through obscurity is not security. The zeroRISC threat model is fully documented and auditable. Our open security architecture means your team can verify every claim we make — and the broader community can find and fix vulnerabilities before adversaries do.
Explore the security model

Deep-tech security should not require a six-month integration project. The zeroRISC SDK exposes a clean, well-documented API that lets your firmware team integrate hardware root of trust functionality in hours, not months. Our primitives are designed to compose cleanly with existing RISC-V toolchains.
View integration docsFrom edge sensors to critical infrastructure, zeroRISC secures the embedded systems that matter most.
The zeroRISC team publishes peer-reviewed research on RISC-V security, root of trust architectures, and verified firmware. Our findings drive the platform forward and contribute to the open security community.
Founded by hardware security veterans with deep RISC-V and silicon expertise.
Technical depth on hardware security, RISC-V architecture, and verified firmware.
A step-by-step examination of implementing a silicon-level root of trust on RISC-V platforms, covering key provisioning, attestation flows, and common pitfalls.
Read MoreExamining why the RISC-V community benefits from transparent, community-audited security architectures over proprietary alternatives.
Read MoreWhy standard secure boot mechanisms fall short for RISC-V embedded systems, and how cryptographic firmware verification changes the security calculus.
Read MoreTalk to the zeroRISC team about your hardware security requirements. We work directly with chip designers, embedded engineers, and infrastructure operators.
Request Access